Navigating Your Account
There are several concepts that are important to understand when navigating your account and structuring your company’s access to Spreedly.
Logging in
To explore your account and manage your company’s access to Spreedly, log in here. If you’re having problems logging in, reset your password from the sign-in page first, then contact us if you’re still experiencing difficulties.
Multi-Factor Authentication (MFA)
We require multi-factor authentication (MFA) using a one-time passcode (OTP) on login as an additional layer of security for your Spreedly account. After entering your credentials and clicking Continue, the OTP is generated by the authenticator application on your mobile device which must be entered into the Spreedly login screen. You can use any authenticator application, including Authy, Google Authenticator, Auth0, or Guardian Microsoft Authenticator. You may also choose to skip entering the OTP again for up to 30 days on your current browser.
To learn more about setting up MFA and troubleshoot any issues, visit our support page.
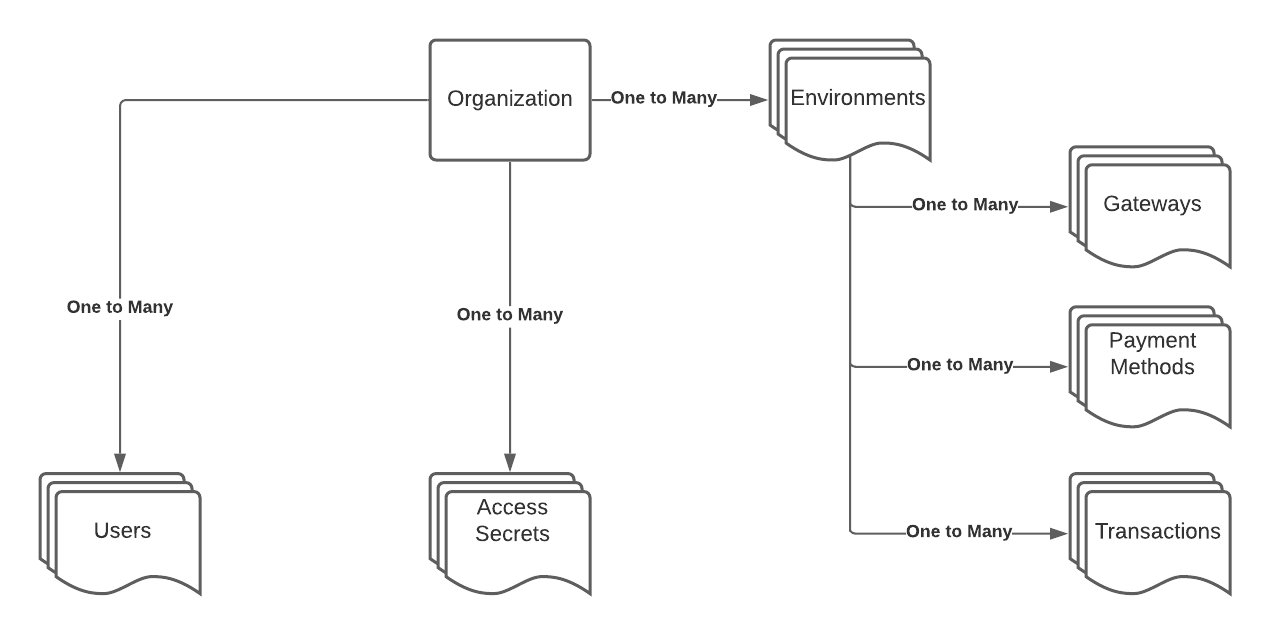
Organizations
Every user on Spreedly belongs to an organization. If you registered for Spreedly directly (i.e., without an e-mail invitation from an existing organization member) you specified the organization name on the registration form.
An organization is meant to represent a complete company and its connected merchant accounts. Billing occurs at the organization level - if groups within your organization have separate billing requirements, they need to operate as independent organizations within Spreedly.
If you are logged into your account, you can change your organization’s name, and more, from the Organization tab.
Adding and removing users
Only add trusted users to your organization. All Spreedly users in your organization have administrator privileges - they can manage and access your list of API access secrets, remove users, cancel your organization’s Spreedly subscription, and take other actions.
To add a Spreedly user to your organization, go to the Users tab when logged into your account. You can invite users via email by clicking the “Add User” button below your list of users. To remove a user from your account, you can click the “Remove” link next to their email address.
A note about removing users: Removing users from an organization prevents that user from accessing authenticated Spreedly websites. However, API access is granted via Access Secrets, which a removed user may have stored elsewhere. We recommend that you rotate Access Secrets when you remove users.
Environments
Each organization can have an unlimited number of environments. An environment allows you to separate your payment information into distinct groups. Note that all environments in paid Spreedly accounts have the capability to make production transactions - there are no test-only environments.
Environments are distinct and should be used to isolate separate payment functions. You cannot use a payment method stored in environment “A” in a purchase against a gateway from environment “B,” for example.
To use the Spreedly API, you must specify an environment key in your calls. An environment key is not sensitive information, so you may safely share it. To find your list of environment keys, visit the Environments tab when logged into your account.
Access secrets
Access secrets are used to authenticate your organization when using the Spreedly API. There are two types of access secrets, a single environment access secret and an organization access secret. A single environment access secret can be used to authenticate API calls for a single environment, while an organization access secret can authenticate API calls for any environment.
To view, create, or delete your single environment access secrets, log into your account and visit the Environments tab. Use Configure for each environment. To view, create or delete your organization access secrets, visit the Organization tab. Alternatively, you can manage single environment access secrets through the Core API.
Best Practices:
Spreedly encourages using single environment access secrets instead of organization access secrets. Using an environment access secret ensures that the access secret will only authenticate API calls for the intended environment. Conversely, any of your organization’s access secrets can authenticate API calls for any environment.
When using organization access secrets, Spreedly recommends using separate environments to isolate production connections and data from non-production connections and data; though there is still risk as production and non-production environments are accessible via a common API access secret. Test and QA environments should not share credentials with production level environments.
Access secrets are considered private and secure. Do not share them or expose them to insecure channels - even in e-mails to the Spreedly team. An access secret, in combination with an environment key, grants full access to the Spreedly API. If you or another user within your organization share an access secret insecurely, we advise that you revoke the secret as soon as possible, and generate a new one.
Spreedly recommends rotating all access secrets every 60-90 days for stronger security. To prevent any downtime, follow these steps in order to rotate an access secret:
- Create a new access secret.
- Update your applications to use your new access secret instead of your original access secret.
- Once your applications have all been updated and the new access secret has been confirmed to work, log into your Spreedly account and delete the original access secret.
For more information on credentials and access secrets, visit our Credentials page.
Diagram